Open Menu
Open Right Panel
A Guide to Trust Frameworks for Smart Digital ID
14 TECHNICAL AND SECURITY RULES
The following Technical and Security requirements support the User and relying party Services and align with the Trust Rules and General Requirements:


14.1 Chain of Trust
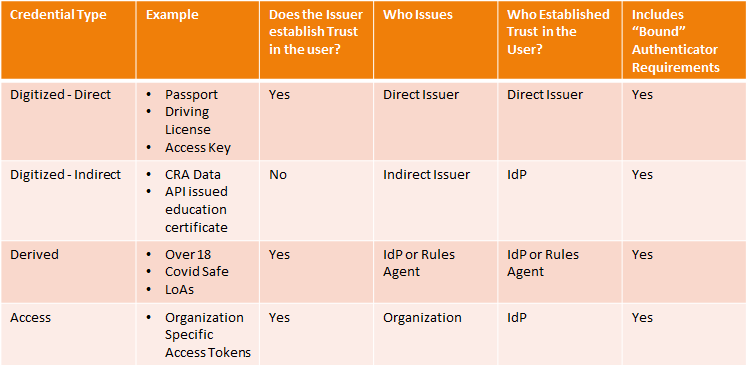
There are two questions that need to be answered when tracing the chain of trust for a credential:
- Who issued the credential?
- Who established trust in the user?
The tracing of trust varies depending on the type of credentials issued. The following table highlights the 4 types of credentials defined in this guide, and how the chain of trust works for each: